Data Protection Starts with Reliable Foundations
Every file, database, and application relies on the same essentials: stable hosting, controlled access, and a recovery path that has been rehearsed. Our work focuses on keeping your critical information available and intact across everyday operations and unexpected incidents, with guidance that is technical, direct, and accountable.
Core Services

Hosting With Performance You Can Measure
Fast, resilient hosting options ranging from dedicated servers to secure VPS environments. Built for flexibility, supported with upkeep and configuration help.
Explore Hosting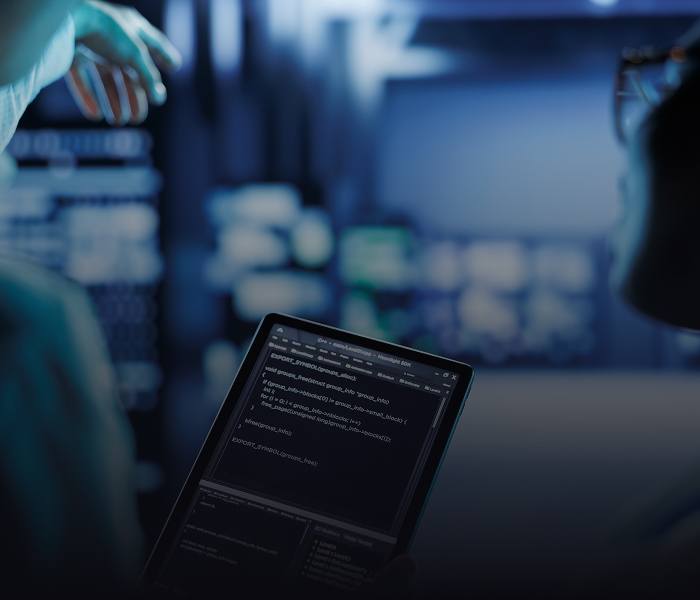
Disaster Recovery That Restores Confidence
Structured recovery planning for cyber incidents, human error, and environmental disruption. We prioritise what must return first and validate recovery steps before pressure hits.
Explore Disaster Recovery
Network Security and Monitoring with Real Visibility
Preventive security controls paired with monitoring that highlights unusual behaviour and access patterns. Gain clarity on what is happening across the network, not guesswork.
Explore Network Security and MonitoringHow We Work

Control Points We Focus On
Access That Matches Responsibility
Identity and permissions are reviewed so that staff and vendors only reach what they need, when they need it.
Backups You Can Actually Use
Retention, encryption, and restore testing are confirmed, with clear recovery time and recovery point targets.
Change Control Without Friction
Updates, configuration changes, and new deployments are tracked so small adjustments do not create hidden failures.
Reporting That Supports Decisions
You receive summaries on health, alerts, and readiness, with next actions prioritised.
Keep Your Business Moving
If you are planning a migration, tightening security, or preparing for a recovery event, Control Solutions can help you take control of the variables that matter. Reach out to discuss hosting, recovery planning, or a vulnerability assessment.
Reach Out Today